Using the qbee-connect tool¶
The qbee-connect tool is a UI based remote access tool that works on Windows, Linux and Mac. It can be downloaded from the "qbee packages" menu item.
The tool maps any remote port to a defined port on localhost (127.0.0.1) on the local system. This way users can get access to remote devices independent if this is an ssh shell connection, a web server, VNC or any other application. It works with TCP and UDP packages and any port or service. The remote service can then be accessed with the mapped port, e.g. localhost:65234.
After installation the user credentials have to be entered into qbee-connect. Then it securely connects to qbee.io and represents the same tree structure that is created in qbee.
Not all users have remote access enabled!
Remote access can be granted by any administrator for any user of qbee. This is defined in the user part of settings. If a user has remote access any remote access attempts will be logged thus giving an effective overview over who has been on different devices.
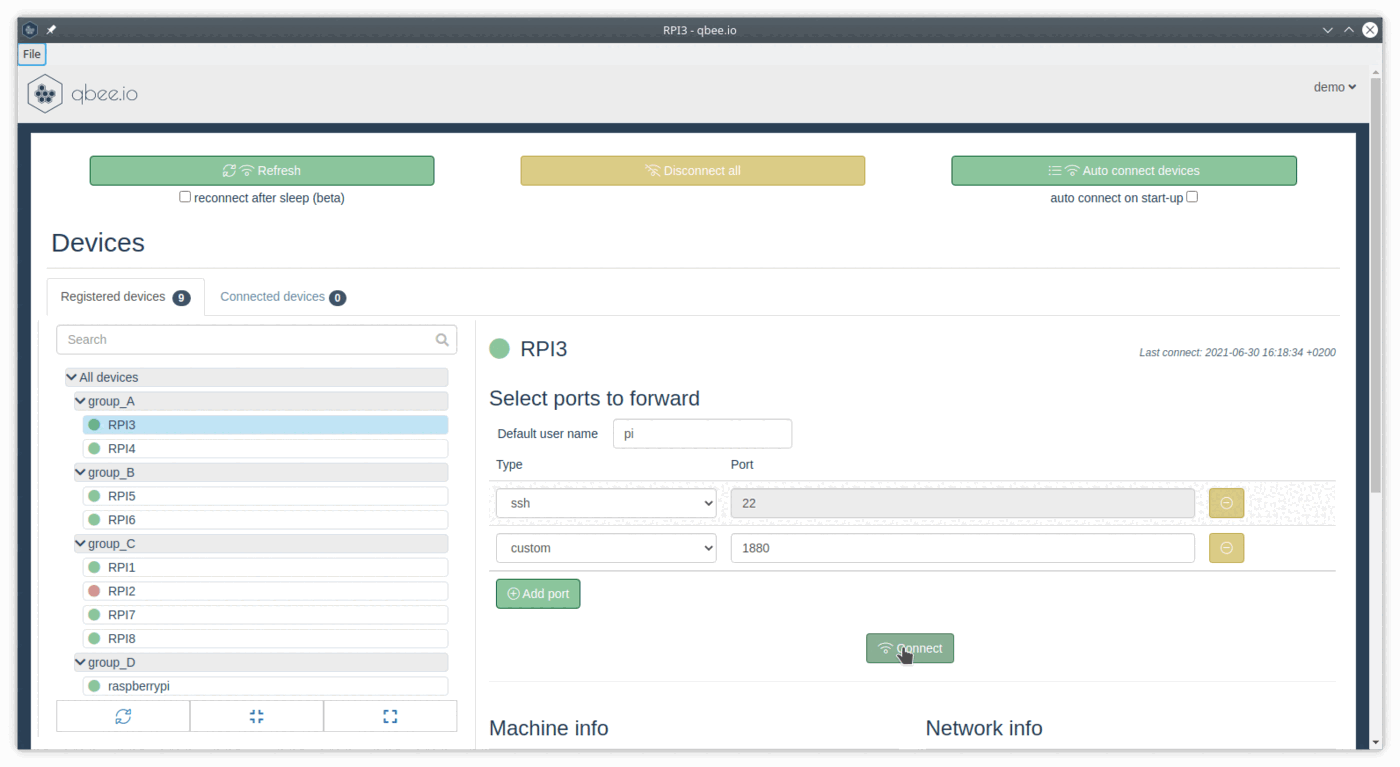
Any device can be selected in the tree on the left. On the right hand side different ports can be selected that will be made available locally. In the displayed example this is ssh with port 22 and a custom port on 1880 (This is a Node-RED server running on the remote device).
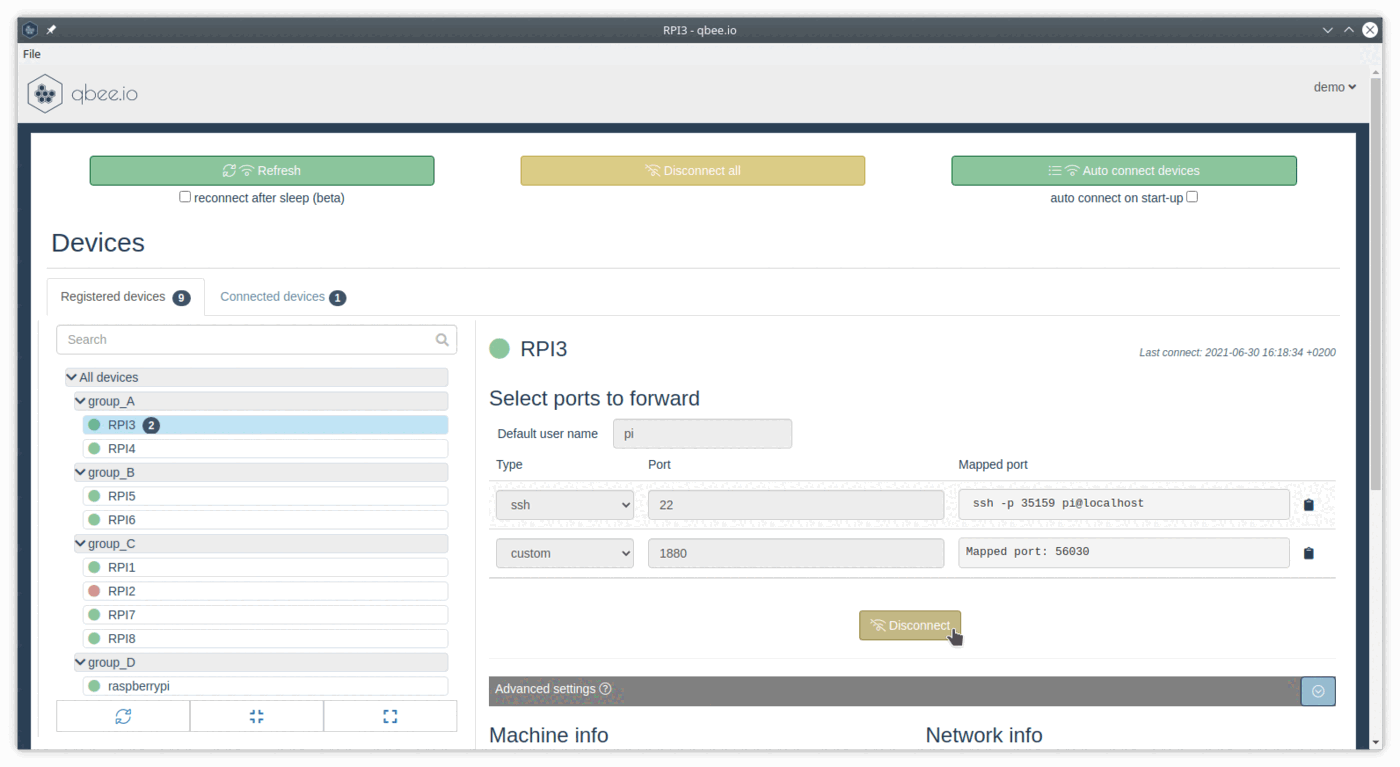
When the connect button is pressed the connection is established. qbee-connect will map the remote ports to random (available) ports on localhost. The mapped port is remembered, i.e. the next time you connect to the remote port you will obtain the same mapped port.
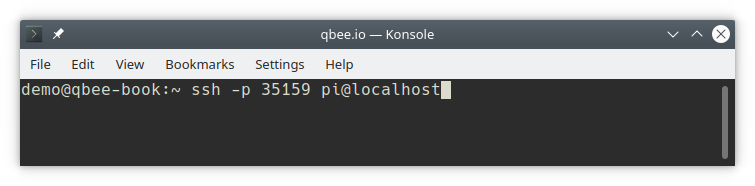
For an ssh mapping the complete command can be copied. The ssh username can be specified under "Default user name" and is included in the command. Paste the command into a regular local terminal, and you can use ssh as usual.
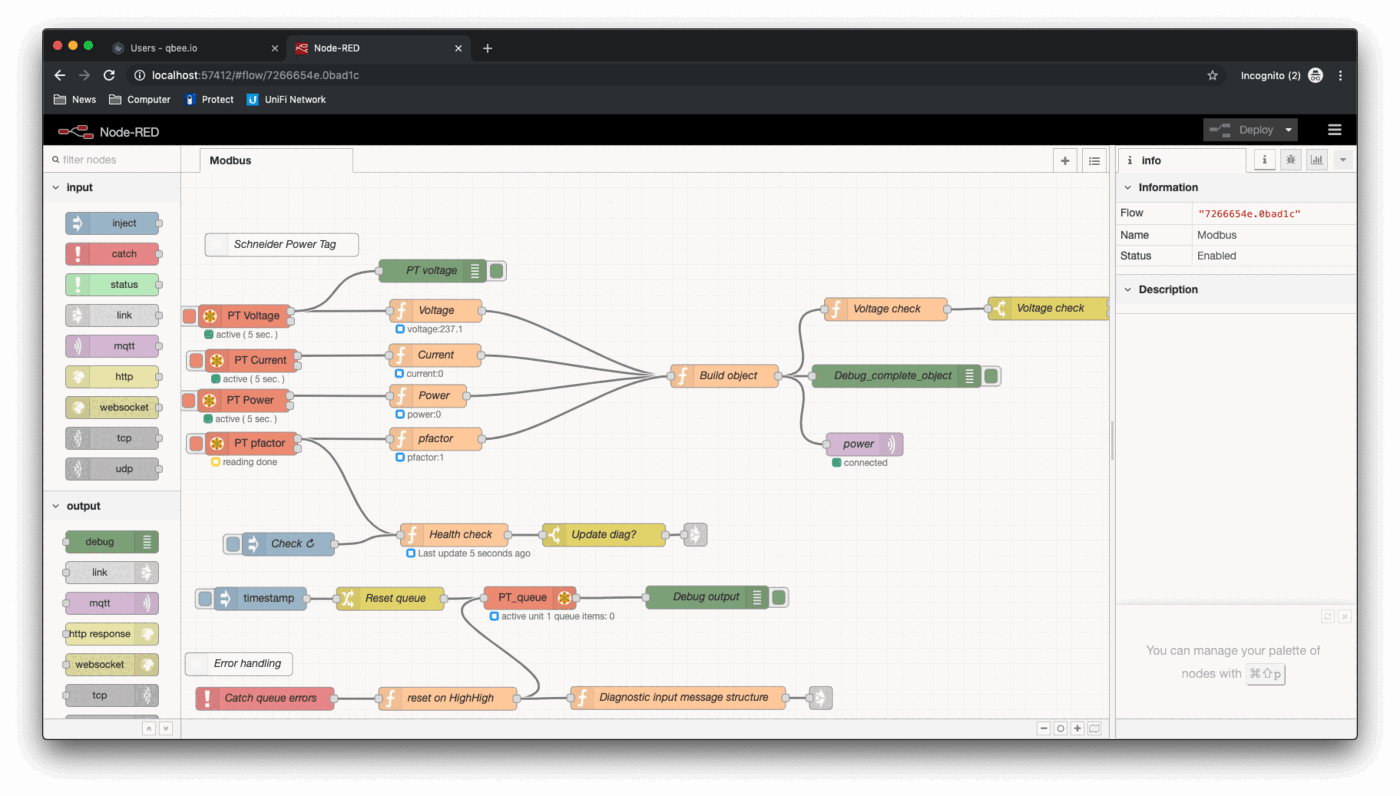
Selecting "http" or "https" always presets port 80 or 443. If you want to use any other port (like 1880 for NodeRED) use custom and define the port. In the example below we are connecting to a remote Node-RED instance with a mapped port of 57412. This gives us full local Node-RED functionality in our browser through remote access.
SSH port forwarding¶
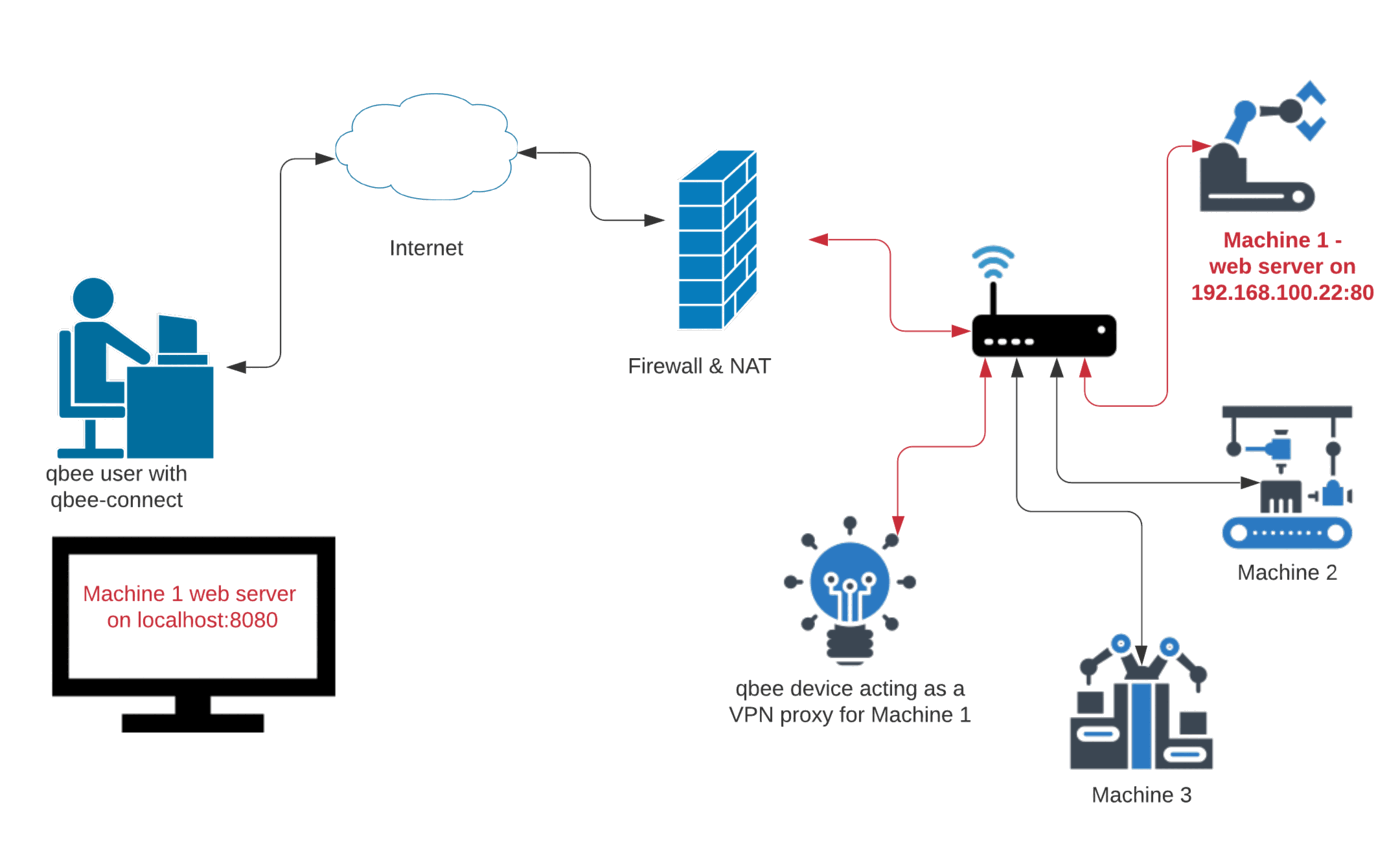
In the following example we show how a web server running on a remote device (see Machine 1 in the diagram below) within the same network as a qbee device can be forwarded to a local machine using ssh.
To be able to forward port 80 of Machine 1 we need to:
- make sure that this port can be accessed through the local network by your qbee device (potentially adjust the firewall settings on Machine 1)
- distribute our public ssh-key to the qbee device for the ssh user (e.g.
piin case of a Raspberry Pi)
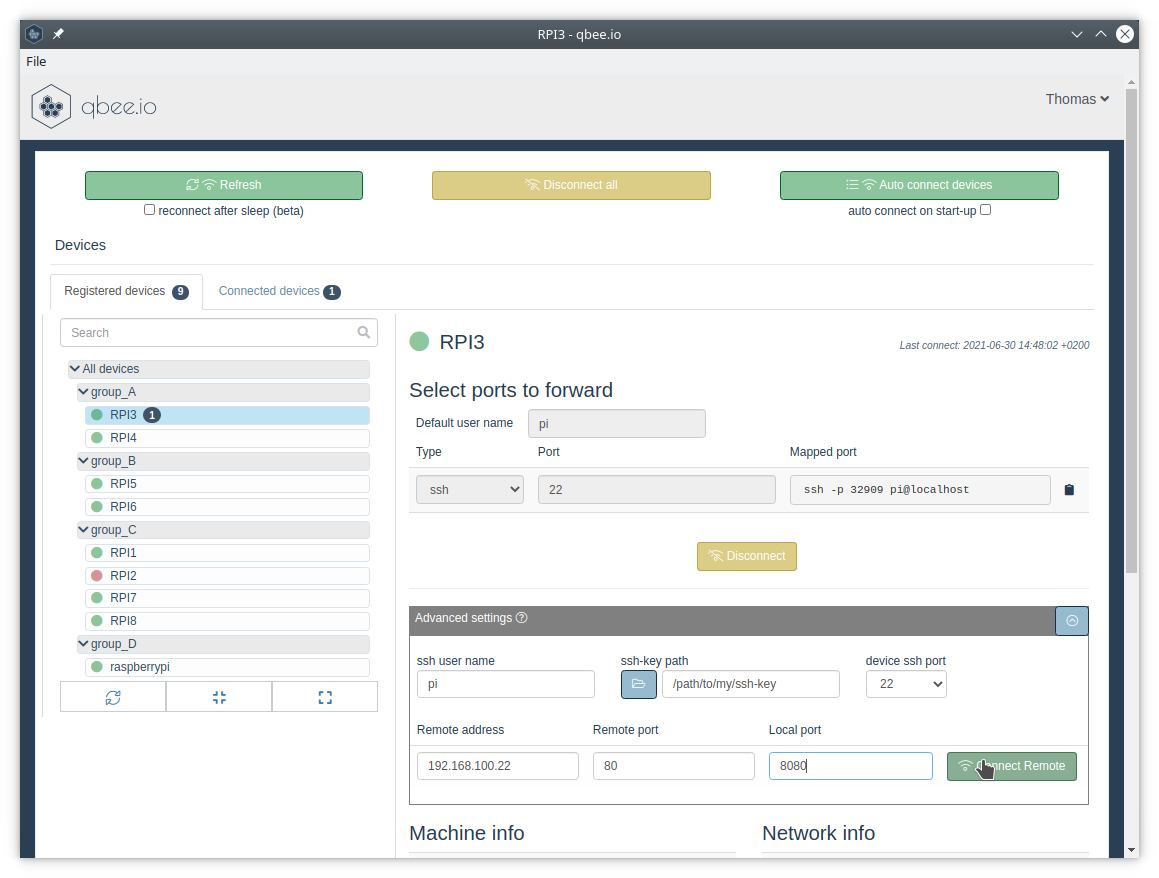
Then within qbee-connect we connect to our qbee device (which is RPI3 in the image below) on the ssh port (here 22). Expand the "Advanced settings" section and fill in the connection information as seen below:
Now we can connect to the remote webserver via localhost:8080 in our browser.
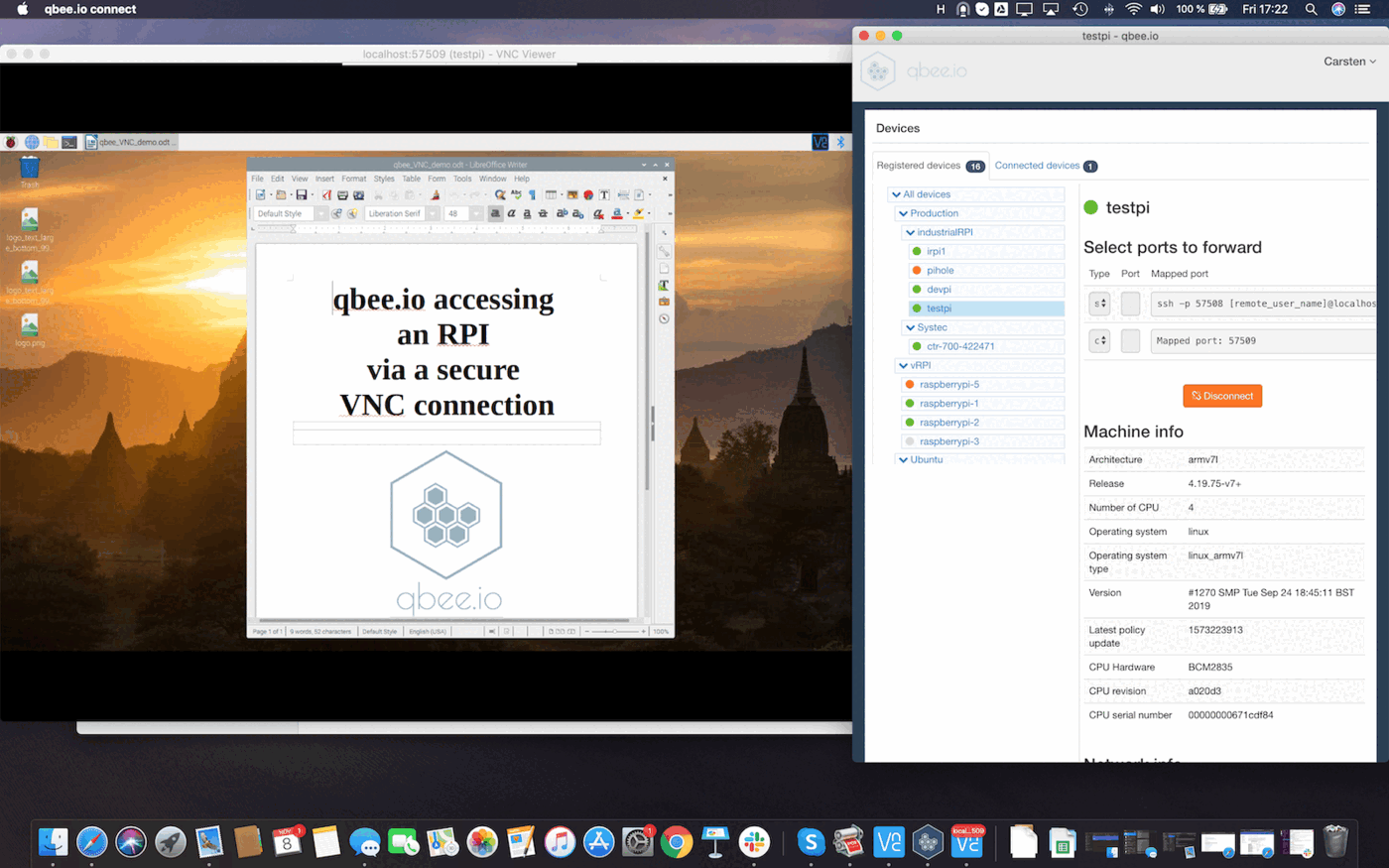
Example - VNC through remote access
Here is another example connecting through RealVNC on port 5900 to get full bidirectional VNC access to a remote device across a firewall with the possibility to control the device with mouse and even upload files. For more information please visit the VNC use case.