Reverse SSH tunneling is a technique used to establish a secure connection from a remote server or a remote IoT device back to a local machine. At its core, it’s about creating an encrypted SSH connection in the opposite direction to the norm. Instead of connecting from a local machine to a remote server, as in traditional SSH connections, reverse SSH tunneling establishes a connection from the remote server to the local machine. This is not a very difficult thing to do and it relies on the ssh tool available in basically any operating system.
The primary use of such a technique is to gain access to a local machine that’s behind a firewall or NAT, without altering those protective measures. It’s especially useful in scenarios where:
Consider two machines: LocalMachine (behind a firewall) and RemoteServer. The goal is to SSH into LocalMachine from RemoteServer. With reverse SSH tunneling, LocalMachine initiates a connection to RemoteServer and sets up a tunnel. Once the tunnel is established, one can SSH into LocalMachine by connecting to the tunnel from RemoteServer.
Setting up this in real life is fairly straightforward if you work with open ports. Here’s a basic example:
ssh -R 9000:localhost:22 user@RemoteServer
Here, 9000 is the port on RemoteServer that will be used for the tunnel, and 22 is the SSH port of LocalMachine.
ssh -p 9000 user@localhost
Ensure that the GatewayPorts option in the SSH daemon configuration file (sshd_config) on RemoteServer is set to yes or clientspecified if you wish to allow connections from external IPs.
While reverse SSH tunneling is a powerful technique, it’s essential to be aware of potential security risks. Ensuring the remote server is secure is paramount since the tunnel could act as an entry point if compromised. Regularly update and patch systems, use strong authentication methods, and monitor connection logs for any unusual activities.
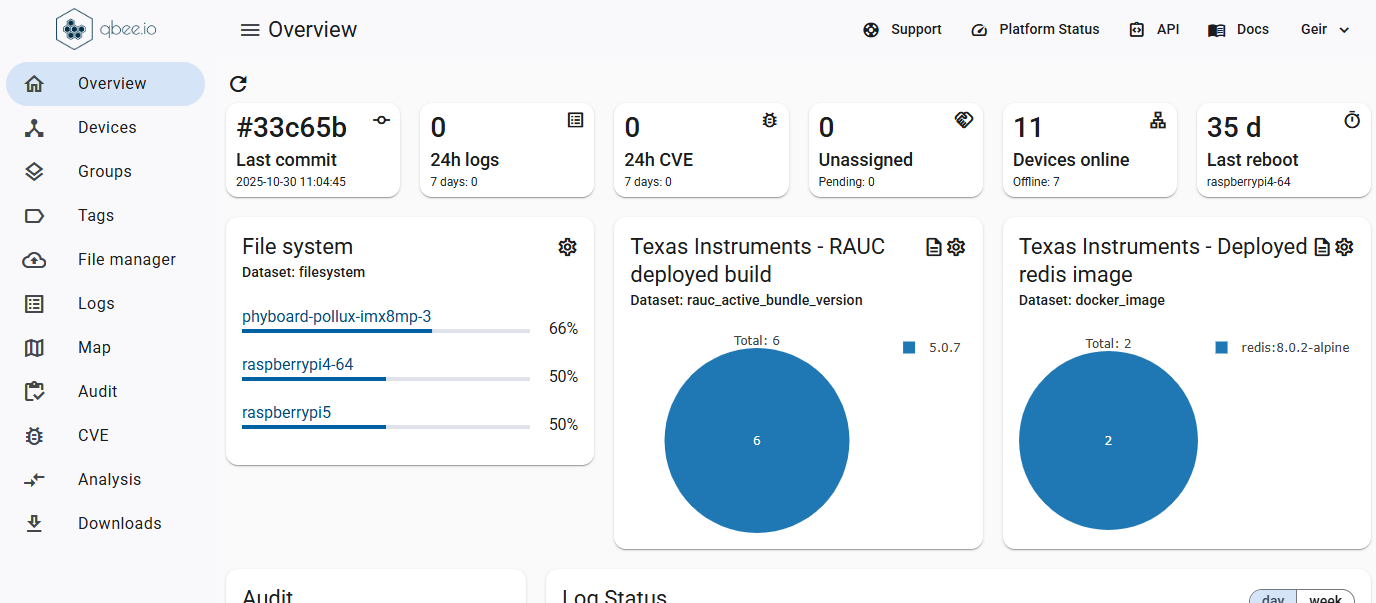
The presented technique offers a way to bridge connections in scenarios where traditional SSH might be limited. By understanding its potential and implementing it carefully, you can harness its power while maintaining security. Whether you’re looking to provide remote support or securely connect machines, reverse SSH tunneling is an invaluable tool in the IT toolkit. If you do not want to build and manage the moving parts of such a solution yourself and you also want the additional security of a properly configured VPN you can try the qbee.io remote device management. This allows you to focus on your use case with a VPN that supports this functionality. In addition, this will get you up and running in less than 5 minutes, no matter if you run desktop machines or IoT devices.