Secure by design
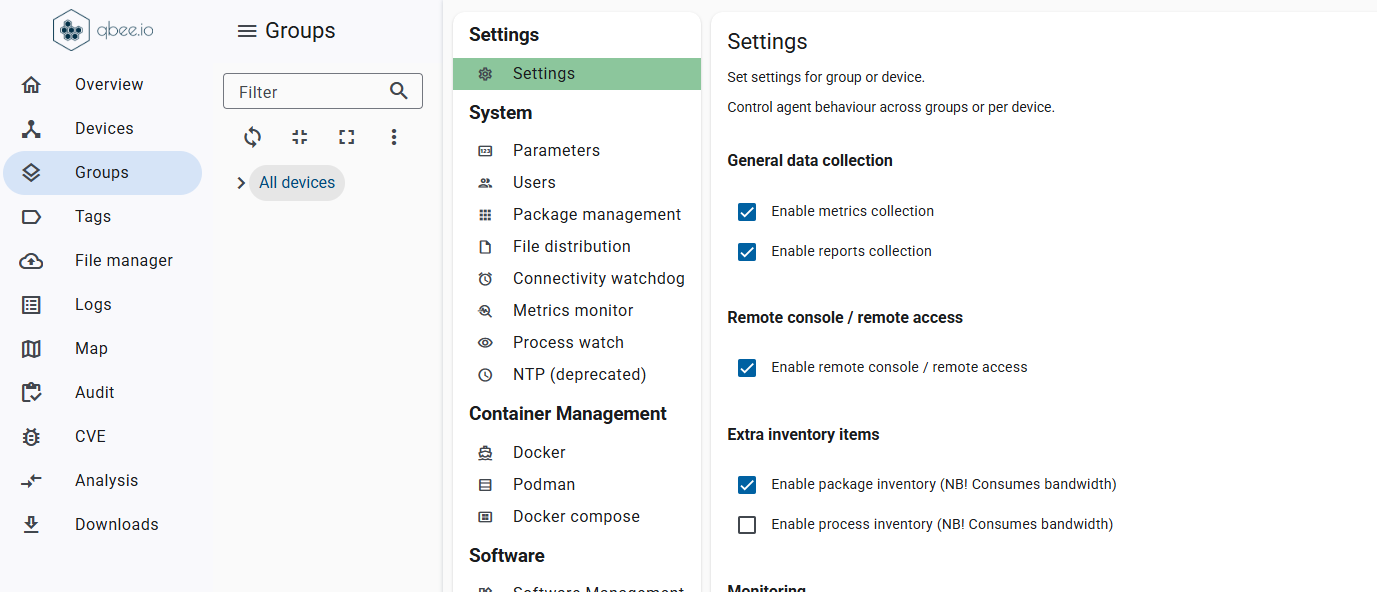
Traditional device management requires exposed services, firewall rules, or inbound connectivity. Each one a potential entry point for attackers. Qbee removes this risk completely.
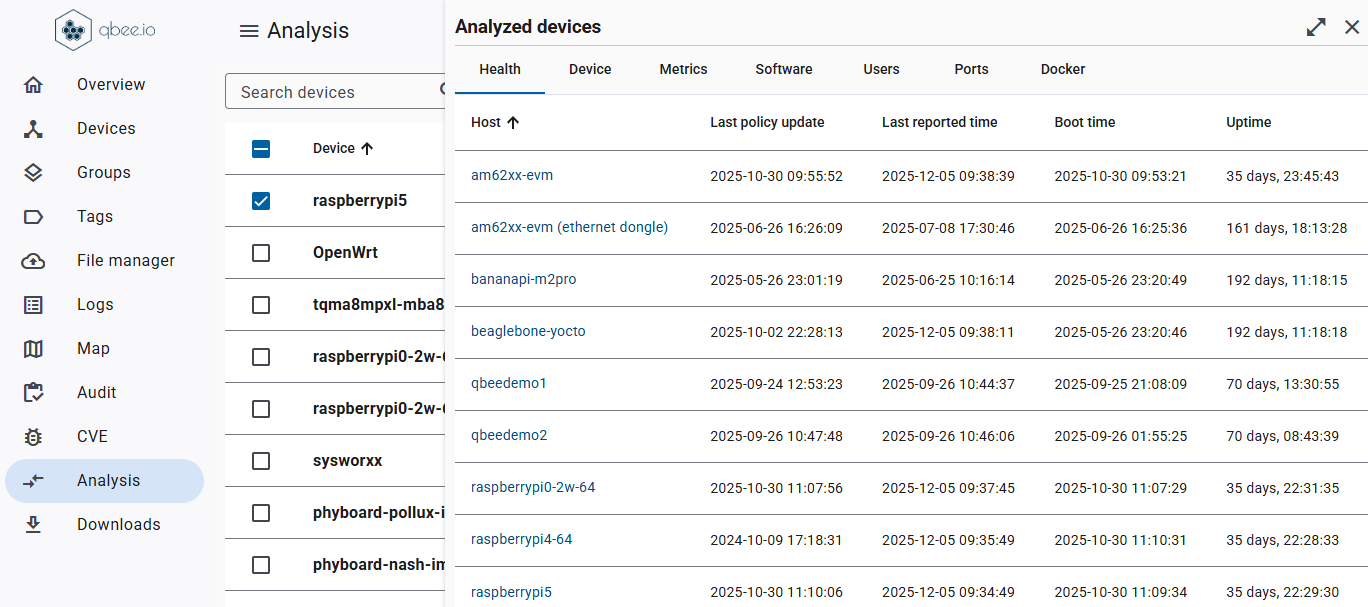
Devices connect outwards only, using a pull-based model that keeps every port closed and the attack surface drastically reduced. This built-in security architecture aligns naturally with CRA expectations for resilient, tamper-resistant products.
Your fleet remains protected even in hostile networks, ensuring your devices stay safe, compliant, and trustworthy from day one and throughout their entire lifecycle.